The keyword 172.16.252.214:4300 often appears in internal systems, server configurations, or application access logs, leaving many users curious about its purpose. While it may look complex, this address follows standard networking principles and plays a critical role in private infrastructures. Understanding how it works, why it is used, and how to manage it properly can help both technical and non-technical users feel more confident when encountering it.
Breaking Down the Structure of 172.16.252.214:4300
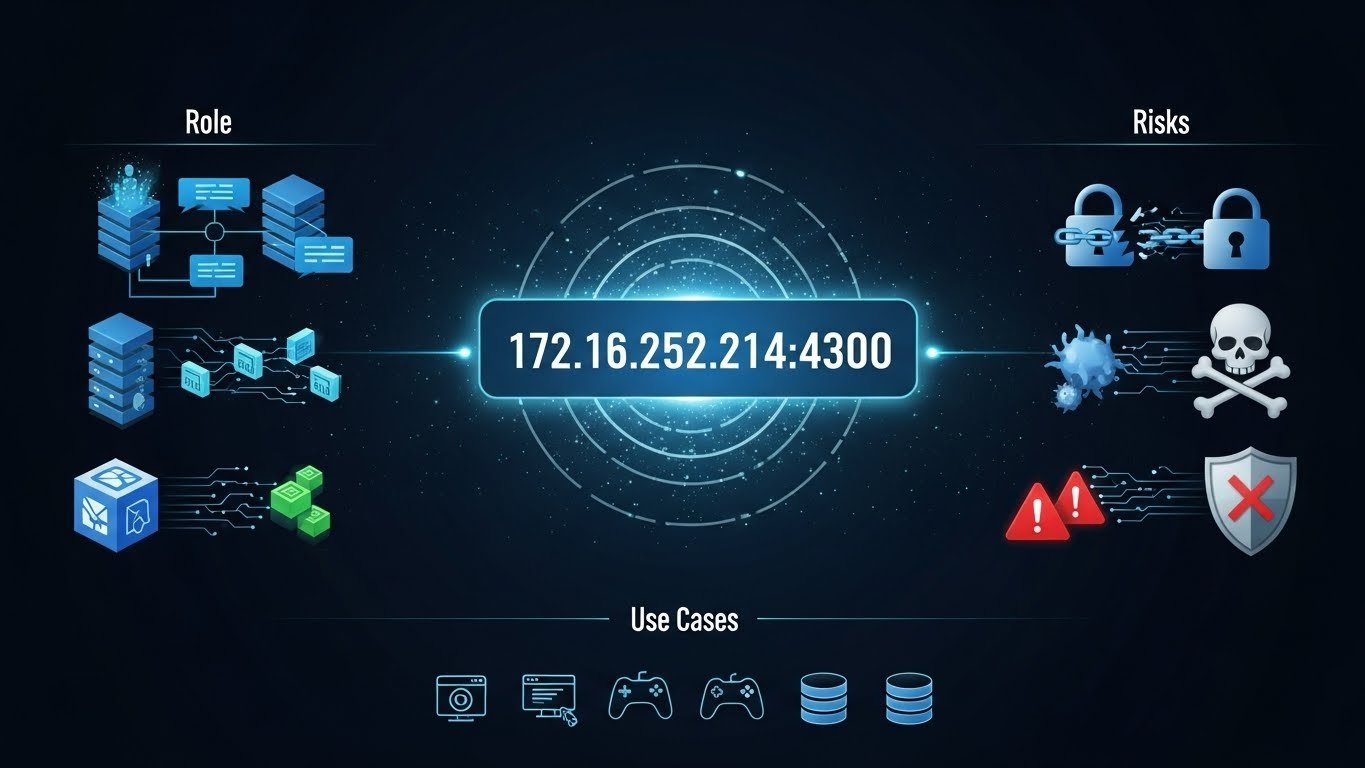
At its core, 172.16.252.214:4300 consists of a private IP address paired with a specific port. The IP belongs to a reserved range designed for internal networks, meaning it is not intended for public internet access. The port number identifies the exact service or application running on that device.
This combination allows organizations to host multiple tools on the same server without conflict. When users access 172.16.252.214:4300, they are directed to a precise application rather than the server as a whole, improving efficiency and control.
Why Private Addresses Like This Are Widely Used
Private addresses such as 172.16.252.214:4300 are preferred in business and development environments because they enhance security and flexibility. Since these addresses are not exposed publicly, they reduce the risk of unauthorized access. Teams can test new applications, manage internal tools, or run experimental services without worrying about external traffic.
In many companies, 172.16.252.214:4300 may serve as a gateway to internal dashboards, analytics platforms, or configuration panels. These tools are essential for daily operations but do not need to be visible outside the organization.
Real-World Applications and Scenarios
One common use of 172.16.252.214:4300 is within software development teams. Developers often assign custom ports to local or staging applications so they can test features safely. This setup allows changes to be reviewed internally before deployment to a live environment.
Another scenario involves system monitoring. Network administrators may run monitoring or logging services on 172.16.252.214:4300 to track performance metrics or detect errors. Because the address is internal, sensitive data remains protected within the network boundary.
Security Practices to Keep in Mind
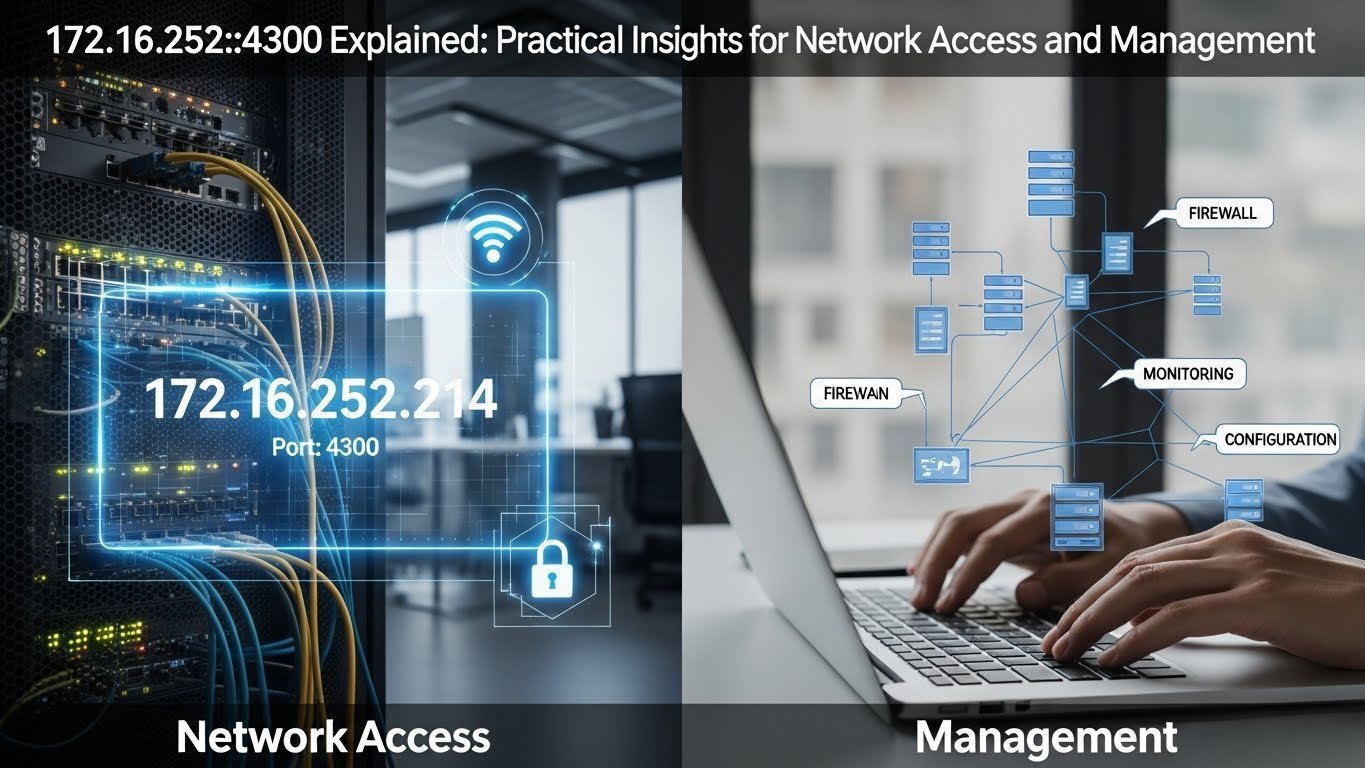
Even though 172.16.252.214:4300 exists in a private range, security should always be a priority. Internal threats, misconfigurations, or compromised devices can still pose risks. Access to services running on this address should be limited to authorized users through authentication and role-based permissions.
Regular reviews of firewall rules and network policies help ensure that 172.16.252.214:4300 is only accessible where necessary. Keeping services updated and disabling unused ports further reduces potential vulnerabilities.
Managing and Documenting Internal Addresses
Clear documentation is essential when working with addresses like 172.16.252.214:4300. IT teams should record which service uses the port, who maintains it, and how it fits into the overall system architecture. This practice simplifies onboarding new team members and speeds up troubleshooting.
Automation tools can also monitor 172.16.252.214:4300 for uptime and response times. Alerts generated by these tools allow teams to respond quickly if a service becomes unavailable, ensuring minimal disruption.
Common Issues and How to Resolve Them
If users report difficulty accessing 172.16.252.214:4300, the issue often lies in network configuration. Incorrect subnet settings, blocked ports, or stopped services are frequent causes. Verifying connectivity and confirming that the application is actively listening on port 4300 are practical first steps.
Credential issues can also prevent access. Ensuring that users have the correct permissions helps maintain both security and usability when interacting with 172.16.252.214:4300.
Conclusion
The address 172.16.252.214:4300 is a practical example of how private networking supports modern digital operations. It enables secure internal access, supports development and monitoring tasks, and keeps critical tools away from public exposure. With proper management, documentation, and security practices, 172.16.252.214:4300 can remain a reliable and valuable part of any internal network.
Meta Description:
Understand what 172.16.252.214:4300 is, how private IPs and ports work, and why they are essential for secure internal networks.
SEO Category: Informational